In mail-server architecture, MX backup is a solution that should be always implemented for redundancy and to avoid emails being returned with errors due to mail-server unavailability.
The working concept is pretty easy: when the mail-server is offline (failure or maintenance), incoming emails are collected and stored in the MX backup and released once the primary mail-server is back online again.
DNS configuration
To work properly, system requires a second MX record in the DNS entry with a lower priority to properly deliver incoming email to MX backup while mail-server is offline.
mail.domain.com MX 10 mail2.domain.com MX 20
Mail-server and MX backup public IPs have to be also set to reflect the designed architecture.
Required packages installation
In order to use yum command to install all required packages, we need to add the RPMforge repository to our system.
# wget http://pkgs.repoforge.org/rpmforge-release/rpmforge-release-0.5.2-1.el6.rf.x86_64.rpm
# rpm -Uvh rpmforge-release-0.5.2-1.el6.rf.x86_64.rpm
In addition to Postfix, the installation process includes additional packages to protect the server from spamming: ClamAV, Spamassassin and Amavisd-new.
# yum install postfix spamassassin clamd clamav-db amavisd-new
Because in this system we want to use only Postfix, if other packages are installed (Sendmail for instance) we need to set the correct MTA through the command alternatives selecting the right option.
# alternatives --config mta
Because in this example only the package Postfix is installed, the number option to type is 1.
If Sendmail is installed in the system, remove it using the yum command.
# yum remove sendmail
ClamAV configuration
Edit the file /etc/clamd.conf and check that communication between Amavisd-new -> ClamAV is made through the local UNIX socket instead of TCP socket.
LocalSocket /var/run/clamav/clamd.sock #TCPSocket 3310
# vi /etc/clamd.conf
Enable ClamAV option removing the #.
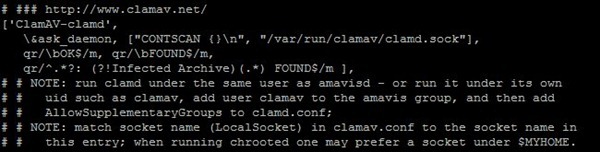
['ClamAV-clamd',
\&ask_daemon, ["CONTSCAN {}\n", "/var/run/clamav/clamd.sock"],
qr/\bOK$/m, qr/\bFOUND$/m,
qr/^.*?: (?!Infected Archive)(.*) FOUND$/m ],
Amavisd-new configuration
Edit configuiration file /etc/amavisd.conf and set the parameters with values that reflect your network environment.
$mydomain = 'nolabnoparty.com'; # domain.com $MYHOME = '/var/amavis'; $helpers_home = "$MYHOME/var"; $lock_file = "$MYHOME/var/amavisd.lock"; $pid_file = "$MYHOME/var/amavisd.pid"; $myhostname = 'mail2.nolabnoparty.com'; # hostname.domain.com
# vi /etc/amavisd.conf
Postfix configuration
Edit the file /etc/postfix/master.cf and add the following lines:
# ========================================================================== # service type private unpriv chroot wakeup maxproc command + args # (yes) (yes) (yes) (never) (100) # ========================================================================== amavisfeed unix - - n - 2 lmtp -o lmtp_data_done_timeout=1200 -o lmtp_send_xforward_command=yes -o disable_dns_lookups=yes -o max_use=20 127.0.0.1:10025 inet n - n - - smtpd -o content_filter= -o smtpd_delay_reject=no -o smtpd_client_restrictions=permit_mynetworks,reject -o smtpd_helo_restrictions= -o smtpd_sender_restrictions= -o smtpd_recipient_restrictions=permit_mynetworks,reject -o smtpd_data_restrictions=reject_unauth_pipelining -o smtpd_end_of_data_restrictions= -o smtpd_restriction_classes= -o mynetworks=127.0.0.0/8 -o smtpd_error_sleep_time=0 -o smtpd_soft_error_limit=1001 -o smtpd_hard_error_limit=1000 -o smtpd_client_connection_count_limit=0 -o smtpd_client_connection_rate_limit=0 -o receive_override_options=no_header_body_checks, no_unknown_recipient_checks,no_milters,no_address_mappings -o local_header_rewrite_clients= -o smtpd_milters= -o local_recipient_maps= -o relay_recipient_maps=
# vi /etc/postfix/master.cf
Edit the file /etc/postfix/main.cf .
# vi /etc/postfix/main.cf
Add the following two lines:
#AMAVISD-NEW content_filter=amavisfeed:[127.0.0.1]:10024
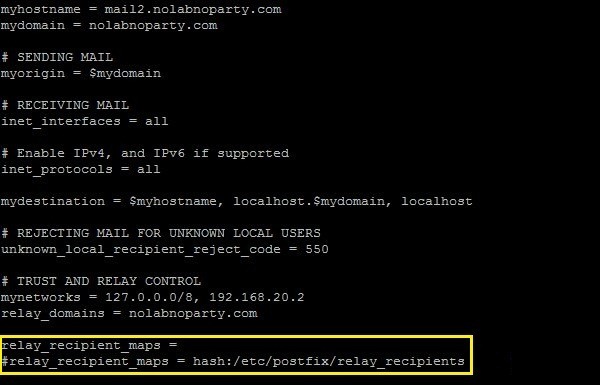
Change the configuration parameters with values that fit with your network environment.
myhostname = mail2.nolabnoparty.com # hostname.domain.com mydomain = nolabnoparty.com # domain.com myorigin = $mydomain mydestination = $myhostname, localhost.$mydomain mynetworks = 127.0.0.0/8, 192.168.20.2 # IP MX backup host relay_domains = nolabnoparty.com # target domain inet_interfaces = all smtpd_recipient_restrictions = permit_mynetworks,reject_unauth_destination relay_recipient_maps = message_size_limit = 0 mailbox_size_limit = 0 maximal_queue_lifetime = 5d
If the relay_recipient_maps parameter is left blank, all the emails are processed by the MX backup regardless if recipients exist or not in the mail-server with the risk of storing also “junk” emails. By creating the file /etc/postfix/relay_recipients with existing accounts, the problem is solved and only emails addresses to existing recipients are kept. Of course if you have a dynamic environment with thousand mailboxes, this approach is perhaps not the best option.
# vi /etc/postfix/ relay_recipients
# Accounts configured in mail-server angus.young@nolabnoparty.com malcolm.young@nolabnoparty.com bon.scott@nolabnoparty.com brian.johnson@nolabnoparty.com cliff.williams@nolabnoparty.com phil.rudd@nolabnoparty.com
Enable installed services to be processed during system startup.
# chkconfig postfix on
# chkconfig amavisd on
# chkconfig clamd on
# chkconfig spamassassin on
Start the services following the correct sequence.
# service spamd restart
# service clamd restart
# service amavisd restart
# service postfix restart
If a warning related to an outdated ClamAV database is shown, you can manually update the signature by using the command:
# /usr/bin/freshclam
Signature is then updated to latest available release.
System test
Once the configuration is completed, we need to test the system to verify its correct functionality checking if emails are properly processed.
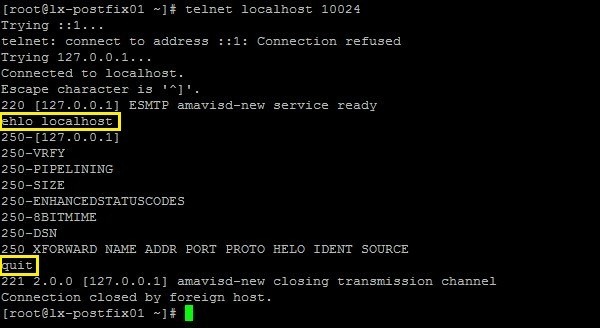
Using the telnet command, we test first if Amavisd service is listening on 127.0.0.1:10024.
# telnet localhost 10024
ehlo localhost quit
Next to test Postfix smtpd service is listening on 127.0.0.1:10025.
# telnet localhost 10025
ehlo localhost quit
Using another computer, connect the MX backup via telnet. In yellow are shown the instructions to enter.
telnet MX_backup.domain.com 25
# telnet mail2.nolabnoparty.com 25
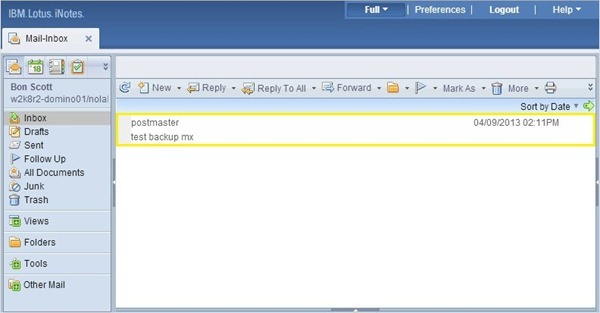
ehlo www.nolabnoparty.com mail from:<bon.scott@nolabnoparty.com> rcpt to:<bon.scott@nolabnoparty.com> data Subject: test backup mx sending message to test backup mx . quit
If the message is delivered to the recipient, then the system is working properly.
If the message is delivered to the recipient, then the system is working properly.
Check Postfix logs activity to verify whether MX backup is processing messages or not.
# tail -f /var/log/maillog
To check the MX backup emails queue, the command mailq shows the messages received so far.
# mailq
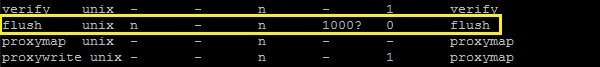
On regular basis the system perform a flush action of queued messages based on the value specified in the /etc/postfix/master.cf file (default 1000 seconds).
# vi /etc/postfix/mastercf
If you don’t want to wait for next flush schedule, a manual flush can be performed using the command postqueue and checking with mailq the queue status.
# postqueue -f
# mailq
When messages are released from the MX backup, if everything works as expected, emails are delivered to the email client.
Instead of buying some cloud resources that could be quite expensive, in the market are available some providers that offer the MX backup service with interesting fees.
With this solution no emails will be lost in case of mail-server failure and scheduled maintenance can be performed taking all the necessary time.