If your corporate policies don't allow you to disable SSH logins to your Hardened Repository, you should add MFA to your system to enforce security.
This protection works only if Veeam Backup & Replications v11 is used since previous Veeam versions required SSH over port 22 breaking the functionality.
To add multi-factor authentication (MFA) to your Hardened Repositories, DUO offers a cost-effective solution that's fit for purpose.
Blog Series
Veeam v11: Hardened Repository (Immutability) installation - pt.1
Veeam v11: Hardened Repository (Immutability) configuration - pt.2
Veeam v11: Hardened Repository (Immutability) add MFA - pt.3
Generate application keys
Before proceeding with Hardened Repository MFA configuration, we need to generate the application keys in the DUO portal.
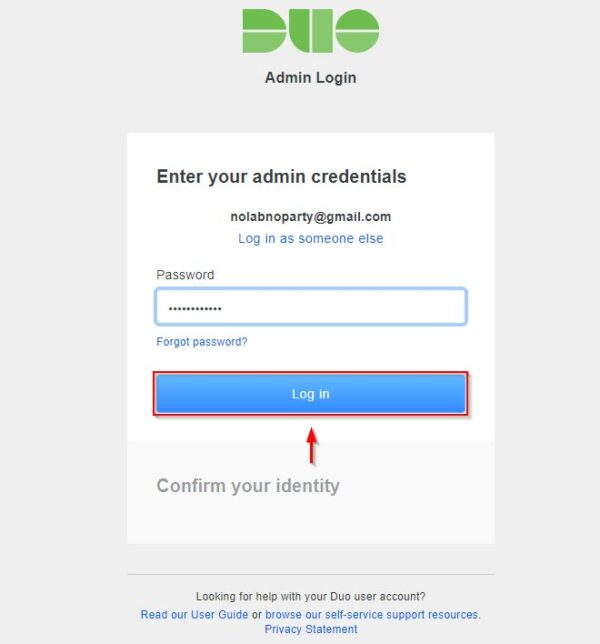
Using your preferred browser, login to DUO portal as admin.
Go to Applications area and click on Protect an Application button.
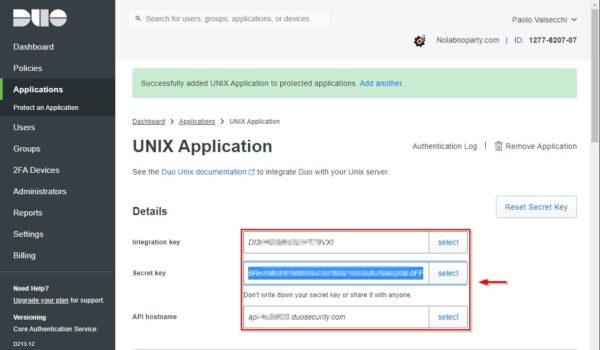
Scroll down the list until you find UNIX Application then click Protect.
Under Details you find the keys to configure duo_login application in your Linux server used as Hardened Repository.
Install login_duo
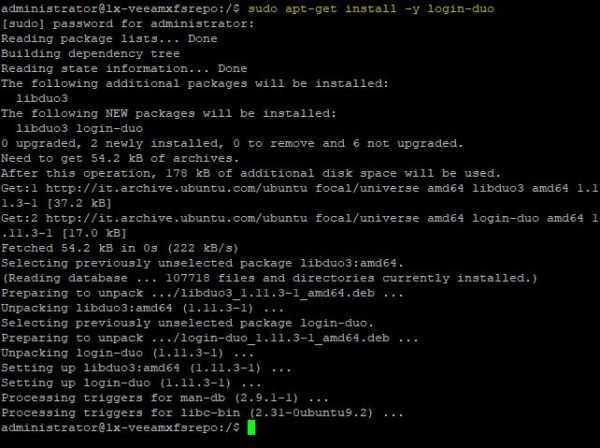
SSH your Hardened Repository and install the login_duo package. In the example, the Hardened Repository uses Linux Ubuntu OS.
# sudo apt-get install -y login-duo
Edit the /etc/security/login_duo.conf file to begin the configuration.
# sudo vi /etc/security/login_duo.conf
Enter the required keys to configure duo_login application. Additional settings can be found in the Duo Configuration Options table.
- Integration key
- Secret key
- API hostname
The /etc/security/login_duo.conf file with the keys generated in the DUO portal.
Test duo_login
As normal user, run the following command to test duo_login. If everything works as expected, you should receive an enrollment link and prompted to enroll.
# /usr/sbin/login_duo
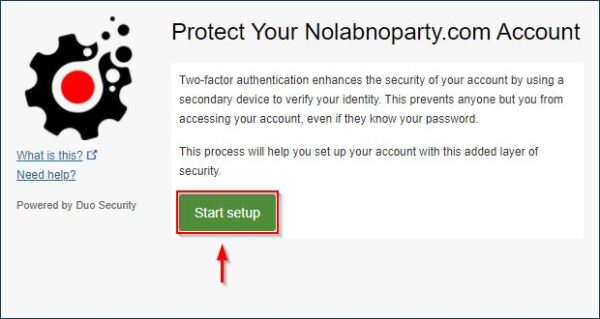
Copy the link to your preferred browser and start the enrollment procedure. Click Start Setup.
Specify the device (Phone recommended) to use and click Continue.
Enter your phone number and confirm. Click Continue.
Specify the phone type and click Continue.
Install DUO app in your phone then click I have Duo Mobile installed.
Using the DUO app installed on your phone, scan the QR code and click Continue when done.
Once the phone has been enrolled, run the login_duo command again. Enter the code displayed in the DUO app installed on your phone and press Enter. If you receive the message "Success. Loggin you in...", the authentication process works properly.
# /usr/sbin/login_duo
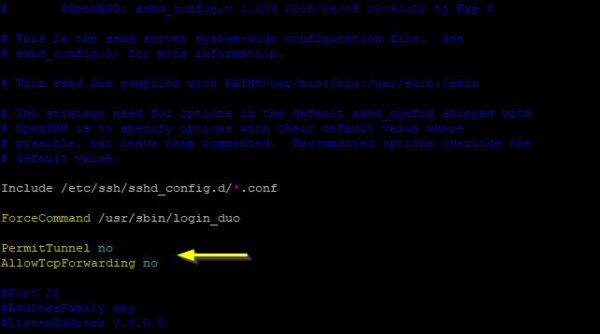
Now, to enable MFA for any SSH login on your Hardened Repository, edit the /etc/ssh/sshd_config file.
# sudo vi /etc/ssh/sshd_config
Add the following line (you need OpenSSH 4.4 or later) and save the file:
ForceCommand /usr/sbin/login_duo
To protect SSH logins, you should disable PermitTunnel and AllowTcpForwarding in your sshd_config. Add these two lines:
PermitTunnel no
AllowTcpForwarding no
Restart SSH service.
# sudo systemctl start ssh
When you try to SSH the Linux Server, you are now requested to enter the passcode generated by the DUO app installed in your phone.
If you want to receive push login request instead of entering the code, add the following line to the /etc/security/login_duo.conf file:
autopush = yes
Although is recommended to disable SSH login, adding the MFA to your Hardened Repository add an extra layer of security.
In addition to adding MFA to SSH logins, make sure there is not direct access to your repository from Internet and block any unwanted inbound traffic. Outbound Internet traffic should allow only DUO, Ubuntu (or the Linux distro you are using) and NTP services.



























Buenas, esto es increbile, monte uno y todo perfecto, solo tengo una duda, y es que al activar el doble factor, cuando una copia de veeam backup se lanza, tambien necesita aprobacion para poder realizarse, ¿hay alguna forma de gestionar eso?
Excellent write up. Thank you very much for the detailed step by step!!!
Thanks! Don't forget to subscribe to the newsletter to stay up to date on new articles.