When an organization suffers a ransomware attack, your systems and data are encrypted with the scope of demanding ransom for decrypting the files.
Without a good data protection strategy, victims of a ransomware attack are forced to pay a ransom to avoid data loss and keep the business alive. What if you pay the ransom and the decryption key is not provided?
Data protection and an effective restore procedure against a ransomware attack are the key to ensure integrity and availability of your data.
The backup strategy
To secure your business data there is only one thing to do, an efficient backup. You must have an effective backup strategy configured in your organization to quickly recover your data in case of problems.
Meet the 3-2-1 backup rule
A working backup is the key for having your data protected and available. If the backup infrastructure configured in your organization meets the 3-2-1 backup rule, multiple copies of your backups are stored in different locations/media (onsite, offsite, tapes) and available to recover.
Use an immutable repository
The use of an immutable repository (local or cloud storage) is the most efficient way to keep your data backup protected against deletion, changes or overwriting. In case of a ransomware attack, the backup files cannot be altered in any way.
You can configure a hardened repository as local Linux-based storage (hardened VA or AMI) or taking advantage of cloud storage solutions such as Amazon S3 with Object Lock or Wasabi.
Backup verification
The backup verification is an important point to ensure your backups are good and can be recovered. This process ensure that backups, replicas and backup copies can be booted properly. The Instant verification feature can be used to check if your backed up VMs can be recovered.
Recover from a ransomware attack
Backing up your data is only the first part of the data protection strategy. You need also a quick way to recover your data in case of site failure or ransomware attack.
If something horribly wrong happens to your VMs, it is essential for the business that all services and data are recovered and made available as quick as possible. Modern software solutions provide all the capabilities that help the administrators to recover the system functionality in a matter of seconds.
Failover to replicas
If the ransomware didn't affect your DR site (if you have one), available replicas can be used to recover the main services with the lowest RTO possible. To ensure availability of your data the Site Recovery capability has been designed to ensure business continuity minimizing services disruption.
To ensure business continuity minimizing services disruption, you must have a working DR plan in place:
- Orchestrate and automate DR: VMs state is continuously verified by Nakivo sending a notification if a VM is unreachable.
- Create multiple Site Recovery jobs: un unlimited number of Site Recovery jobs can be created to serve different purposes.
- Test and update existing Site Recovery jobs: to ensure that a Site Recovery job can be used successfully when a failure occurs, it should be tested on a regular basis to verify its integrity and recoverability. Tests run in an isolated environment without disrupting the production environment.
- Meet your RTO: when implementing a DR plan, the expectations in terms of RTO must be supported by the target infrastructure to avoid unforeseen difficulties.
- Decrease TCO: the Site Recovery feature allows to automate the verification process of recoverability ensuring the required resilience of the infrastructure saving time, effort and costs.
Instant VM recovery
Booting the VM directly from the backup (Instant VM boot) allows to quickly restore the VM functionality without waiting for the restore process to complete. Despite the VM can be booted immediately, the available data are updated to the last backup taken.
Instant granular recovery
The Instant File Recovery is a feature that can be used to quickly restore corrupted or encrypted files and folders.
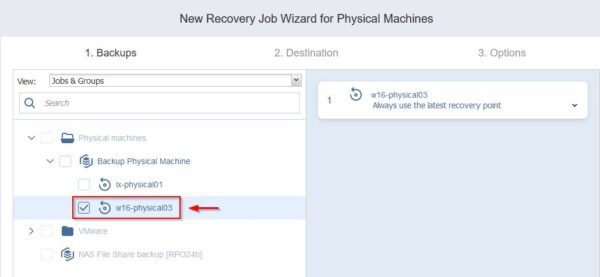
Instant Physical to Virtual Recovery
Physical Windows or Linux servers/workstations can be restored as vSphere virtual machines in seconds without processing the physical machine restore that can take lot of time.
Backup software solutions such as Nakivo Backup & Replication provide all necessary features required to protect your business against ransomware attacks avoiding potential data loss.