A Veeam vulnerability (CVE-2023-27532) has been discovered within a Veeam Backup & Replication that allows an unauthenticated user to request encrypted credentials.
All versions of Veeam Backup & Replication are affected by this vulnerability where an intruder could gain access to backup infrastructure hosts.
Fix for Veeam vulnerability CVE-2023-27532
Patches for Veeam v11a and v12 have been released to mitigate this vulnerability and they should be applied asap.
Patches can be downloaded at https://www.veeam.com/kb4424.
As a temporary fix, you can block external connections to port TCP 9401 in the backup server firewall if no remote components are used (all-in-one scenario).
Install the security patch 20230223
Download the patch and double click the .EXE file to run the wizard.
Click Next to proceed with the installation.
If you receive this error, make sure no processes are currently active and the Veeam console is not open. Click OK.
Select Update remote components automatically option and click Install.
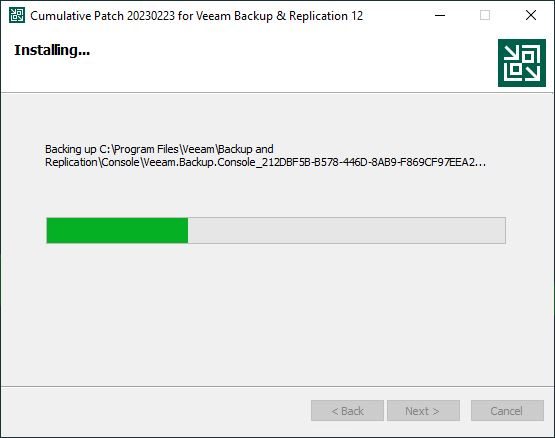
The patch is being installed.
After few minutes the patch installation process completes successfully. Click Finish to exit the wizard.
After installing the patch, the Veeam Backup & Replication build number will be 12.00.1420 P20230223.
To avoid issues, apply the fix immediately to mitigate the Veeam vulnerability.